The term “polymorphic attack” first appeared in the field of cybersecurity in 1990 and describes a new type of computer attack. These nasty viruses are still plaguing computer users, companies, and networks globally more than thirty years later.
Table of Contents
TogglePolymorphic attacks are on the rise in recent times as hackers are coming up with new ways to create spoofed login pages that are almost unidentifiable. This is one of the most frequently used methods by cybercriminals for stealing the credentials of employees and users. The polymorphic attack is now used for a wide range of purposes, including network hijacking, data destruction, information theft, and even the instigation of ransomware attacks.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
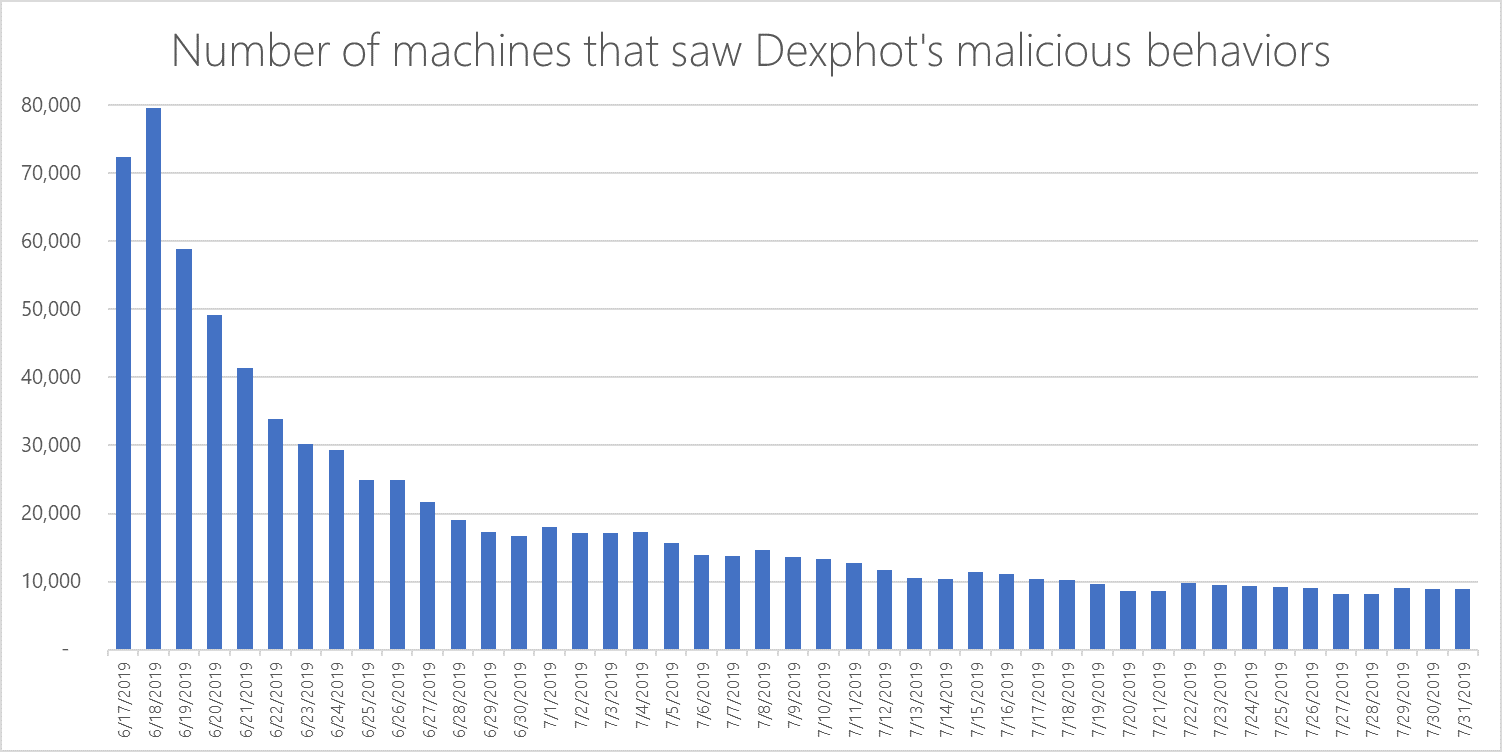
Researchers have disclosed that more than 50,000 spoofed login pages replicating 200 popular international brands have been circulating since 2019. Also, 93.6% of malware has been found to be polymorphic.
This sudden increase in the number of polymorphic phishing attacks is because spoofed login pages are extremely difficult to identify but are comparatively easier to generate by hackers. Automated phishing kits that are illegally sold over the dark web are deployed by cybercriminals to instigate these malicious phishing campaigns and scheme employees on a wider scale. This is why phishing awareness and training have become absolutely imperative in organizations in the 21st century. As a CISO or CIO of your company, taking adequate precautions to prevent polymorphic phishing attacks is the need of the hour.
As per a global survey conducted by security researchers, 42% of all phishing attacks attempted in 2020 were a result of polymorphic attacks.
What is Polymorphic Attack?
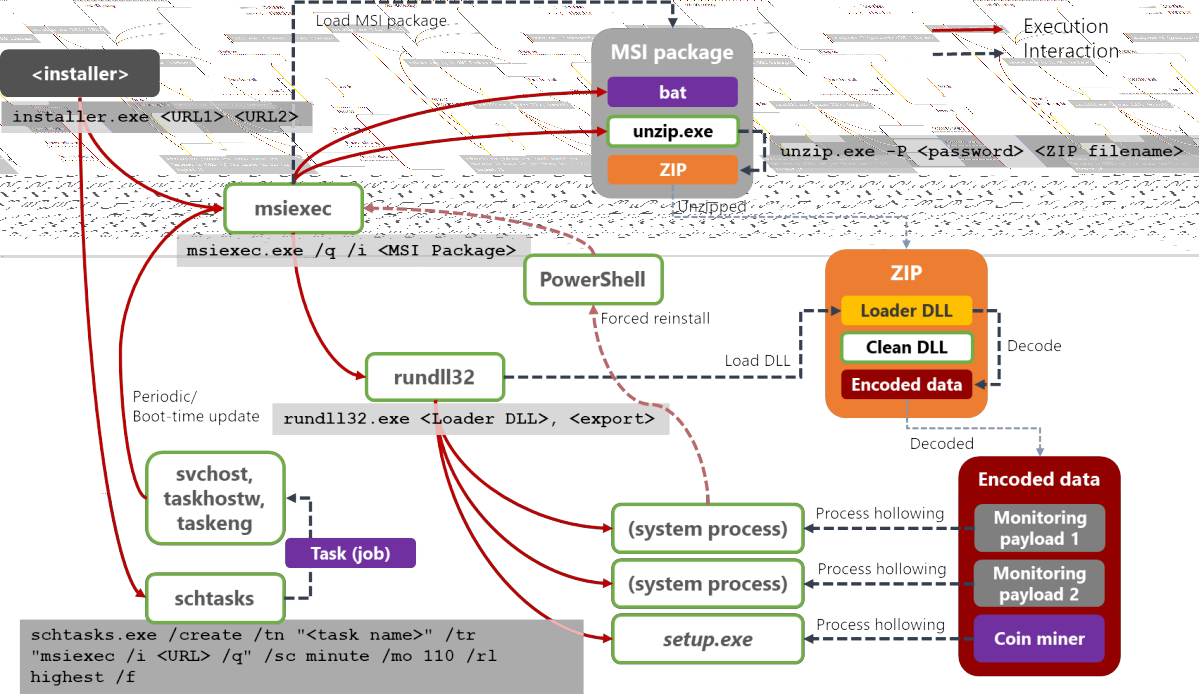
In a polymorphic attack, the virus alters its recognizable characteristics frequently to avoid detection. Numerous prevalent types of malware can be polymorphic, such as viruses, worms, bots, trojans, or keyloggers. Polymorphic techniques frequently alter recognizable traits, such as data files and different kinds of encryption keys, in order to render the malware invisible to many detection methods.
Security tools like antivirus software rely on pattern-matching detection, which polymorphism is used to avoid. Polymorphic malware has some variable characteristics, but it still serves the same functional purpose. For instance, even if a polymorphic virus changes its signature to evade detection, it will still spread and infect devices. The file will not be identified as malicious by signature-based detection tools because its characteristics have been altered to create a new signature. Polymorphic malware can keep going to switch signatures and launch attacks undetected even after being found and introduced to antivirus solutions’ signature database.
Book a Free Demo Call with Our People Security Expert
Enter your details
How to Detect That It is a Polymorphic Attack?
Polymorphic viruses can adapt to nearly any form or appearance. So, it has become quite difficult to identify whether the computer is contaminated with the virus. Administrators can recognize signs of infection by looking for the following:
System Slowdown
When a system slows down unexpectedly or suddenly, it is often a sign that polymorphic malware is attacking it, causing the system to consume more cycles while encrypting files.
Strange Demands
It’s a reliable indication that malware is trying to infect the system or the network when an unusual password request is made. This is when no password has been required in the past. Additionally, users may see strange requests for sensitive details like employee numbers, dates of birth, or social security numbers.
Malpractice
If suddenly a user reaches a URL or website that they didn’t even try to reach, it might be a sign that your computer has malware because it took you to an infected site. Also, an unusual advertisement popping up that blocks a website can also mean that your computer has malware.
Polymorphic Attacks: Prevention and Solution
As a CISO in your company, implementing robust cybersecurity practices in your organization is imperative. To achieve this, security analysts may take help from the IT department and implement security solutions and tools in their respective organizations. A phishing awareness and simulation can help employees gain better insights into social engineering attack vectors. Proper awareness among employees can lower the chances of polymorphic phishing attacks.
Security awareness training starts by simulating sophisticated impersonation attacks on a company’s employees. A number of simulations are conducted to increase security awareness.
After this, the training procedure is initiated by imparting details on the various different kinds of attack vectors. In addition to awareness content, visual presentations on attack identification, as well as video lectures and advisories, are accomplished through awareness content. Regular cumulative assessments are then taken to ensure improvements and initiate a better response against attacks.
Detailed analysis of simulation reports is provided to track results and monitor progress made via assessments and knowledge imparting sessions taken by employees.
In order to prevent employees from falling prey to phishing attacks, it is imperative for CISOs and security officials to implement AI-driven cybersecurity solutions. By upgrading your workplace cybersecurity policy and implementing leading-edge cybersecurity solutions in your company, it is possible to ensure protection against polymorphic phishing attacks.
The most probable reasons for the increase in the number of spoofed login pages may be due to the following two reasons:
- CISOs, CIOs, and SOC analysts of a reputed brand whose landing page has been spoofed seek ways to take the fake pages down. This makes the hackers create more new pages so that they can continue to spoof employees. CISOs and CIOs ensure cybersecurity for their organizations.
- Certain brands or companies may be easy targets for cybercriminals due to the lack of a well-rounded workplace security policy in their organization. This is the reason why attackers get away with polymorphic phishing attacks.
