Key Takeaways
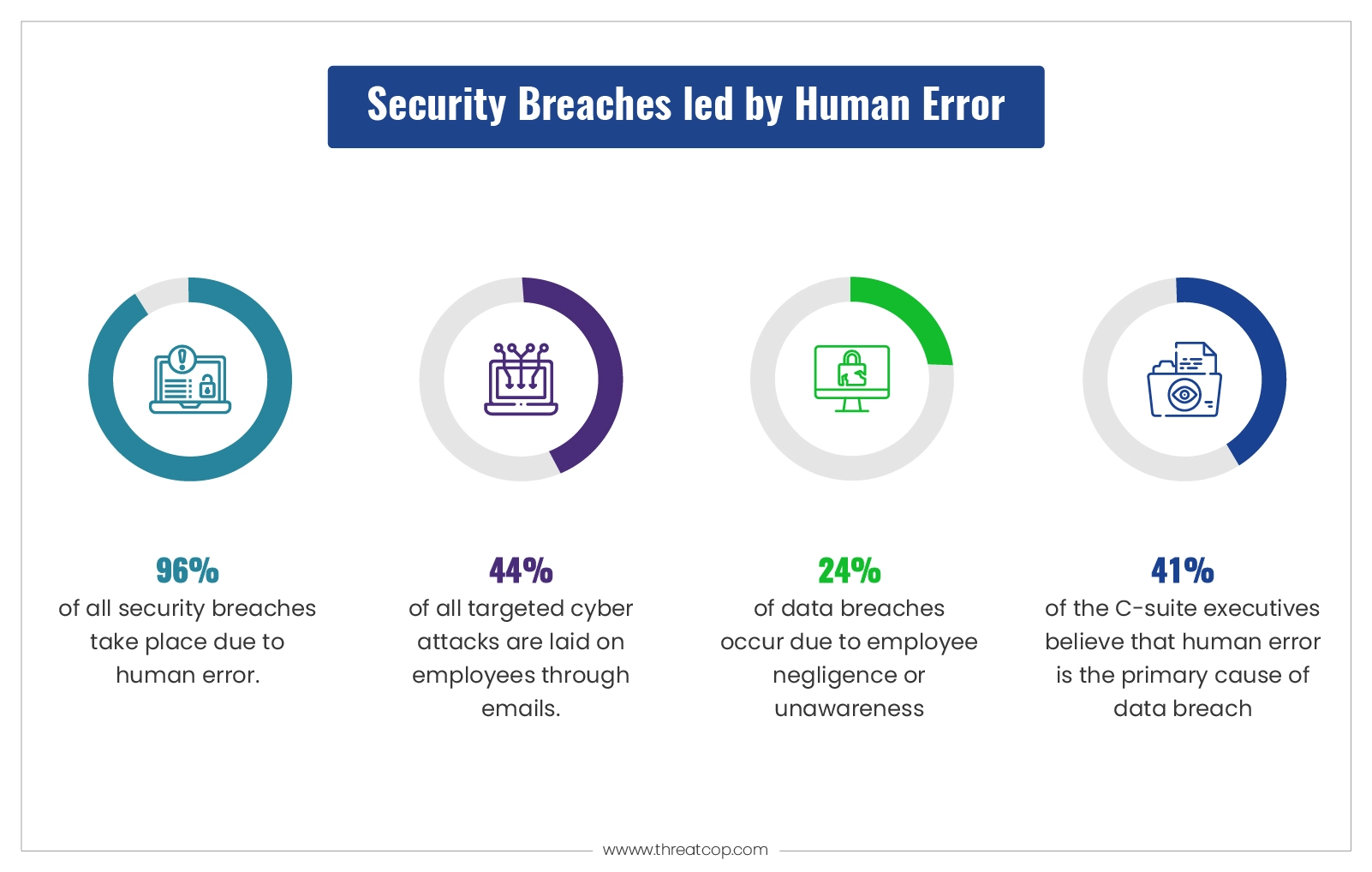
- Human error continues to drive many large-scale cyber breaches.
- Simple actions like clicking malicious links or sharing access can trigger serious incidents.
- BEC and social engineering attacks succeed by exploiting trust rather than technology gaps.
- Even mature security programs fail when employee behavior risks remain unmanaged.
- Ongoing awareness training and realistic simulations significantly reduce human-driven risk.
Most cyber-attacks don’t even start with complex code. They start with a man making an error
Table of Contents
ToggleThe reason that the majority of today‘s successful cybersecurity attacks are of human origin. Clicks on phishing sites, insecure databases, and fake-fund wire orders are accepted without suspicion. These are not anomalies. They are the number one cause of data breaches across sectors and continents.
The figures prove it. IBM’s Cost of a Data Breach Report 2025 states that the average breach cost worldwide is $4.88m, and for US-based companies, it is $10.22m. The human factor was seen in 60% of confirmed breaches in Verizon’s 2025 Data Breach Investigations Report. Even more worrying is that, according to Mimecast’s State of Human Risk 2025, only 8% of employees are responsible for 80% of all security incidents within an organization.
More budget. Better tools. And yet breaches continue to grow. The gap is not technical. It is human.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
Why Human Errors in Cybersecurity Keep Happening
Knowing what the realistic threats to workers already make possible is equally important as identifying the common mistakes employees commit.
Three factors drive most human errors in cybersecurity:
- Cognitive overload. Staff are inundated with hundreds of emails, requests, and decisions every working day. It is impossible to study every single communication in detail. Attackers know this. Phishing emails and Business Email Compromise requests are crafted to arrive in the moments when we are the least alert. Keepnet Labs research suggests 51% of staff make security mistakes when tired.
- AI-assisted attacks. This is something new. The phishing mail of 2025 no longer has the grammatical errors that at least some of us used to notice. AI-generated messages are grammatically correct, conversational, and personalized. Voice cloning and deepfake videos make impersonation attacks look no different from the real thing. The threshold at which we are deceived has come down greatly, whether someone is skilled or not.
- The awareness-action gap. Many organizations realize the risk. Many organizations are effectively managing that risk. Mimecast discovered that while 96% of organizations realize their defenses are not perfect, only 28% combine ongoing staff awareness training with continuous monitoring. Knowledge is not the same as readiness.
These three factors show why these five examples below occur within well-equipped organizations. This is not a startup or a small business, but an existing business with already implemented security measures.
How Do Security Breaches Occur? The Most Common Human Errors
Security breaches may not originate from malware. Most of all starts with a behavior gap.
The greatest human mistake, which is most often exploited, takes the form of phishing. Employees end up clicking on fake links or attachments, giving the hacker their credentials or even direct access to their system.
Business Email Compromise (BEC) attacks accounts and financial and accounting staff with fake e-mails or the identities of hidden individuals to force staff to transfer funds. According to the FBI IC3 Report 2024, BEC attacks Cost $2.77 million in just one year.
Misconfiguration is to leave data lying around, putting files in the wrong location, leaving cloud storage accessible to everyone, or setting the wrong access levels. Verizon has shown that misdelivery and misconfiguration account for over half of the reported errors in the breach datasets.
Weak or reused passwords enable mass credential stuffing and account takeover. According to IBM, stolen credentials are involved in 53% of data breaches and are detected on average 292 days later.
Unpatched systems expose known vulnerabilities to exploitation. Attacks on unpatched systems are often quick once a vulnerability is publicly disclosed and an attacker is looking for one.
5 Major Cybersecurity Breaches Caused by Human Error
There have been numerous high-profile cyber attacks and security breaches caused by human error, bringing several renowned organizations to their knees. So, here are the top 5 examples of how a reckless mistake costs a successful company so dearly.
1. Strathmore Secondary College
In August 2018, an employee at Strathmore Secondary College accidentally published student records for more than 300 students on the school’s intranet, which is accessible to all students and parents. The published records revealed highly sensitive information about students with conditions like ADHD, acquired brain injuries, Asperger’s, and Autism. These records also included information on whether students were on medication, receiving government support, or having treatment plans. In this case, a grave human error exposed immensely sensitive information about hundreds of students.
Book a Free Demo Call with Our People Security Expert
Enter your details
2. Pennsylvania Department of Education
In February 2018, an employee in the Pennsylvania Education Department’s Office of Administration made an error that compromised the state’s Teacher Information Management System (TIMS). The TIMS database contains personal information about teachers who apply for and hold teaching certifications in Pennsylvania. The compromised database temporarily enabled anyone who logged in to access the personal information of other users, including teachers and staff from school districts and the Department of Education. This security breach, caused by human error, affected around 360,000 current and retired teachers.
3. Toyota Boshoku Corporation
A European subsidiary of the Toyota Group, Toyota Boshoku Corporation, suffered a massive BEC attack in August 2019 that cost the company $37.3 million. On 14th August 2019, the auto parts supplier was tricked into making a large fund transfer into the hackers’ bank account. The threat actors posed as a subsidiary’s business partner and sent carefully crafted emails to members of the accounting and finance departments. These emails requested that the funds be sent to a specific bank account controlled by the hackers. Soon after the transfer was made, the company’s security experts realized that they had been duped. However, by then, it was too late to stop the transfer.
4. Sequoia Capital
Known for being one of Silicon Valley’s oldest and most notable venture capital firms, Sequoia Capital was hacked in February 2021. Among the major recent cyberattacks due to human error, this hack exposed some of its investors’ personal and financial information to a third party. The cyberattack succeeded when one of Sequoia’s employees fell for a phishing attack. Focused on energy, enterprise, financial, healthcare, mobile, and internet startups, this VC firm has more than 1100 corporate clients in addition to over 200 international clients.
5. Leoni AG
In 2016, a leading wire and cable manufacturer, Leoni AG, was scammed out of $44 million by a devastating BEC attack. Cybercriminals impersonated the company’s senior German executive to send emails to an employee working in the finance department of the company’s factory in Bistrita, Romania. The email was carefully crafted using inside information to look perfectly genuine and requested a transfer of $44 million from the company’s bank account. It tricked the employee into making the payment, and the stolen funds were transferred to a different bank account in the Czech Republic.
Tools to Reduce Human Error in Cybersecurity
Training reduces the frequency of errors. Technical controls reduce the impact when errors still occur. Both are necessary. Neither alone is enough.
Security Awareness Training: TSAT runs simulated phishing, vishing, smishing, and ransomware campaigns that test employees under realistic conditions. Employees who fail a simulation receive immediate, targeted training at the moment of failure, when retention is highest. Research shows that consistent security awareness training reduces phishing click rates by up to 86%. Threatcop LMS supports this with role-specific modules, assessments, and measurable vulnerability tracking across departments, so leadership can see risk reduction over time.
DMARC and Email Security: TDMARC prevents attackers from sending email using a trusted domain by enforcing DMARC, SPF, and DKIM authentication. It gives organizations full visibility into who sends email on their behalf and blocks unauthorized senders at the source. Both Toyota Boshoku and Leoni AG were compromised through domain spoofing. DMARC closes that entry point directly.
Multi-Factor Authentication: Microsoft reports that MFA blocks 99.9% of automated account compromise attacks. Passwords get stolen. MFA ensures that a stolen password alone is not enough to gain access. It should be mandatory for all accounts, especially those with financial or administrative access.
Zero Trust Architecture: Zero Trust removes the assumption that anyone inside a network is automatically trusted. Every access request is verified continuously, regardless of origin. Unusual behavior, such as an unexpected login location, bulk data download, or an out-of-pattern fund transfer, triggers alerts in real time. This does not rely on an employee recognizing a threat. It catches what humans miss.
Phishing Incident Response Threatcop TPIR gives employees a one-click mechanism to report suspicious emails immediately. Fast reporting is one of the most underrated controls in cybersecurity. The faster a phishing email is flagged, the faster it can be neutralized across the entire organization before others open it.
How to Prevent Cybersecurity Breaches Caused by Human Error
The five cases above were not caused by inadequate technology. They were caused by people who were either untrained, deceived, or operating without guardrails around their actions.
Stopping human errors in cybersecurity requires two things working together: a trained workforce and technical controls that catch the mistakes training does not prevent every time.
Continuous, role-based training replaces annual checkbox sessions with relevant, ongoing education. Finance teams practice spotting BEC attempts. IT teams train on misconfiguration and phishing. Executives receive targeted awareness for whaling and CEO fraud attacks. Generic training leaves specific teams dangerously exposed.
A blame-free reporting culture is often the difference between a contained incident and a full breach. Employees who fear punishment delay reporting mistakes. That delay turns a manageable error into a catastrophe. Fast, honest reporting consistently limits breach impact. Build a culture where reporting is rewarded, not penalized.
Technical controls that do not depend on humans to work. MFA, DMARC, PAM, and Zero Trust function whether an employee is distracted, tired, or deceived. These are not replacements for training. They are the second line of defense when training is not enough on a given day.
How Can Threatcop Help?
Threatcop TSAT provides organizations with a comprehensive platform to simulate real attacks, train employees at the point of failure, and track measurable risk reduction over time. It covers phishing, vishing, smishing, ransomware, and WhatsApp-based threats using attack scenarios built around current methods, not outdated templates.
Paired with Threatcop LMS, organizations build a continuous learning environment using advisories, videos, newsletters, and role-specific quizzes. Pre- and post-simulation assessments provide leadership with concrete evidence of improved security.
TDMARC handles email authentication, domain spoofing prevention, and visibility across all outbound email, directly addressing one of the most exploited attack vectors in BEC fraud.
FAQs
How do security breaches occur through human error?
Most cybersecurity breaches caused by human error happen through phishing attacks, misconfigured access permissions, BEC fraud, weak or reused passwords, and unpatched software. Attackers design campaigns specifically to exploit these patterns.
What are the most common human errors in cybersecurity?
The most frequent human errors are falling for phishing emails, approving fraudulent wire transfers, misconfiguring cloud storage or access permissions, reusing weak passwords, and delaying software patches.
Can employee training alone prevent cybersecurity breaches?
Training significantly reduces risk but is most effective when combined with technical controls. MFA, DMARC, and Zero Trust catch errors that training alone cannot stop every time.
Cyber Security Specialist
Department: Compliance, Threatcop
Sara Abraham is a Cyber Security Specialist at Threatcop, where her extensive expertise in the field is instrumental in strengthening the company’s cyber security initiatives. She is a key contributor to the company’s mission of providing top-notch security solutions.
Cyber Security Specialist Department: Compliance, Threatcop Sara Abraham is a Cyber Security Specialist at Threatcop, where her extensive expertise in the field is instrumental in strengthening the company's cyber security initiatives. She is a key contributor to the company's mission of providing top-notch security solutions.
