Anxiety, stress, fear, shock, etc., are the terms that have always been used in medical science to emphasize psychological issues or disorders. But similar things have seeped into the cybersecurity domain in the form of “Scareware Attacks.” This attack works by creating panic and a sense of urgency among the users to download software that is infected with malware.
Table of Contents
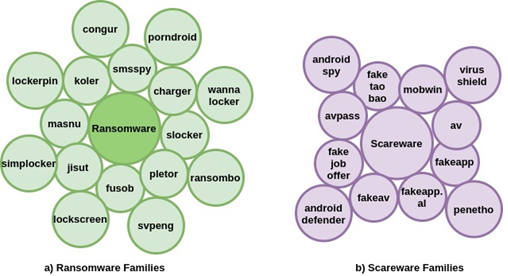
ToggleNumerous cyber attacks are carried out using malware, and each of them is characterized by the approach of the attack. For example, when data is stolen by infecting the system with malware and a ransom is demanded, it is known as ransomware. Similarly, if malware gets injected and monitors all the activities of users and delivers it to attackers, then it is spyware.
What is a Scareware Attack?
A scareware Attack is a malware attack that is carried out by threat actors using social engineering tactics. They target users in general by displaying ads or pop-ups on specific websites, scaring them that their computer systems are vulnerable.
Users are enticed to purchase useless software, download malware-infected software, visit websites that automatically download malware into the system, and so on. The notion of social engineering tactics being used in this attack is to create a sense of urgency and claim that the data of users is in a vulnerable position.
Book a Free Demo Call with Our People Security Expert
Enter your details
Scareware is a scam where people are manipulated to believe that they are in some kind of threatening situation. For example, some sites immediately show an ad of users being traced and direct them to download software so that they can protect themselves. Such software is more likely to contain malware or threatening scripts.
According to the FBI’s IC3:
- Tech support frauds accounted for a $54 million loss in 2019. The number of complaints filed in the US was 13,633.
- The report by IC3 also shows that in the same year, scareware attacks incurred losses of $2,009,119
Malware’s Role in This Attack
The term ‘malware’ refers to malicious software. Malware is a kind of software, as a whole or sometimes a part of the software, whose purpose is to damage or destroy computer systems. Various forms of malware are quite popular nowadays, such as worms, spyware, Tofsee malware, trojan horses, adware, ransomware, etc.
These types of malware are very infamous because of direct attacks or the scale of damage they incur on the systems. While in many other cases, these programs are fitted into some other software or file system. When that software or file system is executed, then these scripts are also executed.
The role of malware, specific to scareware attacks, is based upon the fact that the user is fearful or scared and needs to install a particular software. That software is malicious as it contains some kind of script that is intended to incur a breach in the security system or give unauthorized access. The messages or information relayed by scamware scammers, direct the user to procure software or tech services that are inclusive of malware scripts or programs.
Difference between Scareware and Ransomware
The activities that are considered to be ransomware are basically infecting the system with malware and procuring information. This information is later traded for a huge amount of money from organizations. The ransomware is purely carried out through phishing or other tactics that involve getting credentials or bypassing security.
But in the case of a scareware attack, it’s employees’ unawareness and fear that leads to the attack. The notification or advertisement showing the system in a vulnerable position creates a sense of fear among the users. That’s why the stated actions lead them to download malware unknowingly, leading to the compromise of data from the systems.
Impact of Covid-19 on Malware Attacks
Covid-19 started to impact the global cybersecurity infrastructure in early 2020. The pandemic’s most significant contributing factor was the global fear environment. This fear manifested itself not only biologically, but also in cybersecurity systems, which became vulnerable to cyber attackers. In the meantime, many infamous and humongous cyberattacks took place, causing panic in the cyber world.
Threat attackers used this pandemic as an opportunity to carry out cyber attacks which can be categorised under scareware attacks. These attacks involved malicious actors sending caution messages or ads to users. These caution messages portrayed covid-related threats to users, and they were lured into a malicious campaign. They were asked to install certain software or PDFs that had the necessary precaution measures or information regarding Covid-19.
Like such situations, the unaware or frightened users often download malware unknowingly and fall victim to cyberattacks.
Popular Scareware Attacks
The scareware methodology is equally used by cyber attackers and scammers to lure and scam users. It provides a mechanism for persuading people to buy software or download something that is actually not essential. Below are some popular examples of scareware scams.
Tech Support Scam by Support.com
According to a report by the Federal Trade Commission (FTC), a tech support company whose website was support.com was carrying out a scareware scam. In 2019, they were fined $35 million in settlements with the FTC. This settlement is meant to pay back the scammed users. This website was providing diagnostic services which generated false alarms about the security and health of the system. Then it offered users the option to purchase services to repair the issues.
Scareware Attack on the Minneapolis Star Tribune Website
According to the US Department of Justice (DOJ), a guy claiming to be a part of a scareware hacking scam pleaded guilty. Between May 2009 and June 2011, Peteris Sahurovs was a part of a tech support fraud ring that targeted the visitors of the Minneapolis website. Sahurovs informed the DOJ that he had received $250,000 upfront for his involvement for over a year.

How to Prevent Scareware?
- Precaution and awareness are the best preventative measures against cyber attacks.
- A user must be cautious about pop-ups or banners that they see on the websites.
- They should be able to comprehend which ads could lead them to harm.
- They must avoid installing or downloading security software or just checking up on software from unauthorized sources.
- Always use authorized software for scanning threats or prevention of them.
If a user observes any kind of ad or pop window asking them to take a certain action, then they must close the whole window rather than just clicking on close or cancel. Also, one must not accept any technical support from unknown security services.
How to Remove Scareware?
- The most common malware attacks usually take place on mobile devices. So, in the case of malware detected on a phone device, it must be reported to device administration to get a security patch, or if the damage is imminent, the device must be reset.
- Apart from that, in computer systems, malware can get injected and get activated after some time. In such cases, the antivirus or anti-malware employed in the system must be updated periodically.
In the worst-case scenario, the only option is to erase the memory. This is done when anti-malware software is unable to resolve the issue or remove the malware. That’s why multiple layers of security are employed within the hardware of the system to make sure that malware doesn’t get into the system.
The Solution is to Raise Awareness
People get more fearful when they are unaware of certain things. A malware attack is conducted because people get frightened of certain instances such as virus detection in the system, location tracking, etc. This allows the attackers to allure users by providing them with a medium as a resolution. This situation is extremely sensitive for employees in the organisation as it can put the organization’s cyber system at risk. That’s why every organisation needs to carry out cybersecurity awareness training for their employees. This will enable them to become more vigilant and cautious about such manipulative acts of instilling fear in their victims and luring them into a cyberattack.
