Have you wondered what is the biggest reason for the majority of security breaches? You must be wondering, if they are remote access tools, malware attacks, vulnerability exploitation, etc. But it might come as a surprise to you that CISOs/CIOs worldwide are majorly concerned about their employees as the prime medium for security breaches. That’s why they put immense effort into educating and training their employees to defend the social engineering attacks, which are carried out because of human error and employee negligence. That’s where Threatcop’s unique approach, People Security Management (PSM) comes in assistance for security leaders. Let’s explore how!
A study carried out by Stanford University in collaboration with a cybersecurity firm found that employees’ mistakes are the causes of 88% of data breaches. Similarly, IBM published research citing that 95% of security breaches occur due to human error.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
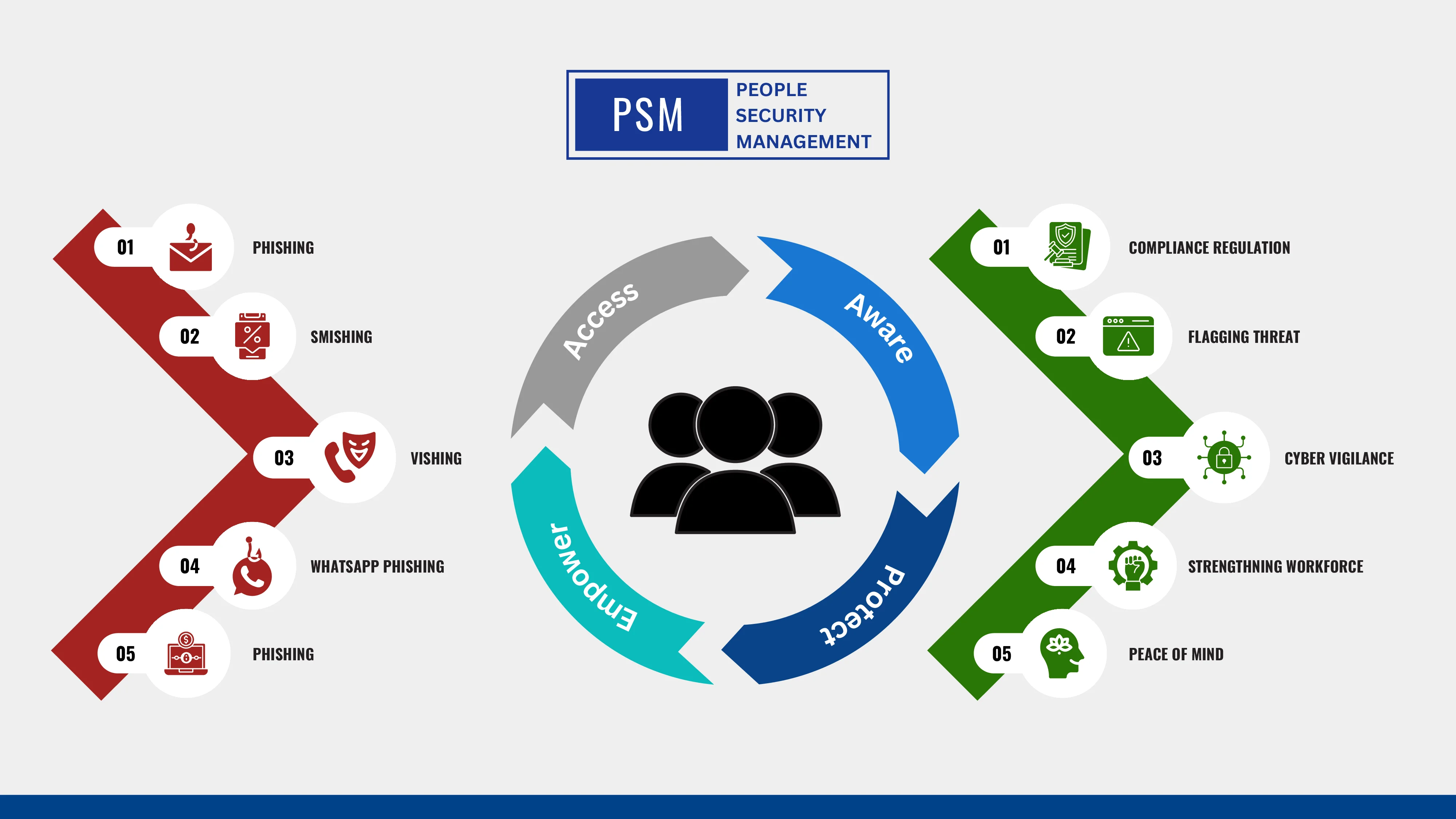
With a keen understanding of the human element in cybersecurity, Threatcop offers innovative tools and solutions based on the AAPE model: Assess, Aware, Protect, and Empower. Our exclusive AAPE model sets us apart, Assessing the weakest links, raising Awareness, providing robust Protection, and Empowering employees to defend against cyber threats. From assessment and training to incident response and employee empowerment, Threatcop is poised to revolutionize the way organizations approach PSM, enabling them to stay one step ahead of cyber threats while harnessing the power of their most valuable asset—their people.
At Threatcop, we are committed to supporting and enhancing People Security Management for our valued customers. Through our four major products – Threatcop Security Awareness Tool (TSAT), Threatcop Phishing Incident Response (TPIR), Threatcop Learning Security Management (TLSM), and Threatcop Domain-based Message Authentication, Reporting & Conformance (TDMARC)– we follow a comprehensive approach to assess, raise awareness, and empower organizations in their cybersecurity endeavors.
1. Threatcop Security Awareness Tool (TSAT)
Research by IBM found that 95% of cyber security vulnerabilities are due to human mistakes. In other words, 19 out of 20 cyber breaches might not have happened at all if human error were completely eradicated. These facts are enough to address the need for employees’ security awareness training.
Employee awareness training educates on potential countermeasures a threat actor could use. The instruction includes instances of affected workers as well as details on numerous assault channels. Additionally, the training imparts information and awareness of cybersecurity procedures, such as how to create secure passwords and secure credentials, etc. With TSAT, you can also simulate and inform your employees about smishing attacks, with our smishing prevention tool.
TSAT Covers the following types of training
Every organization should implement the following awareness training programs. Educate your employees about multiple attack vectors via different types of training methods. This will assess your people’s security posture by identifying and prioritizing risks.

Phishing Awareness Training
Did you know that 92% of malware is delivered through email?
Phishing attacks, a common form of social engineering, rely on tricking individuals into revealing sensitive information by pretending to be someone trustworthy. Phishing awareness training aims to educate employees about the tactics used by cybercriminals to lure unsuspecting victims. It helps employees understand the various techniques employed by cybercriminals and equips them with the knowledge to avoid falling victim to such scams.
Vishing Awareness Training
Vishing is a voice call phishing scam where cybercriminals manipulate individuals over the phone to divulge confidential information or share OTPs. Vishing awareness training educates employees about the different ways these attacks can occur and helps them avoid falling prey to misleading phone calls.
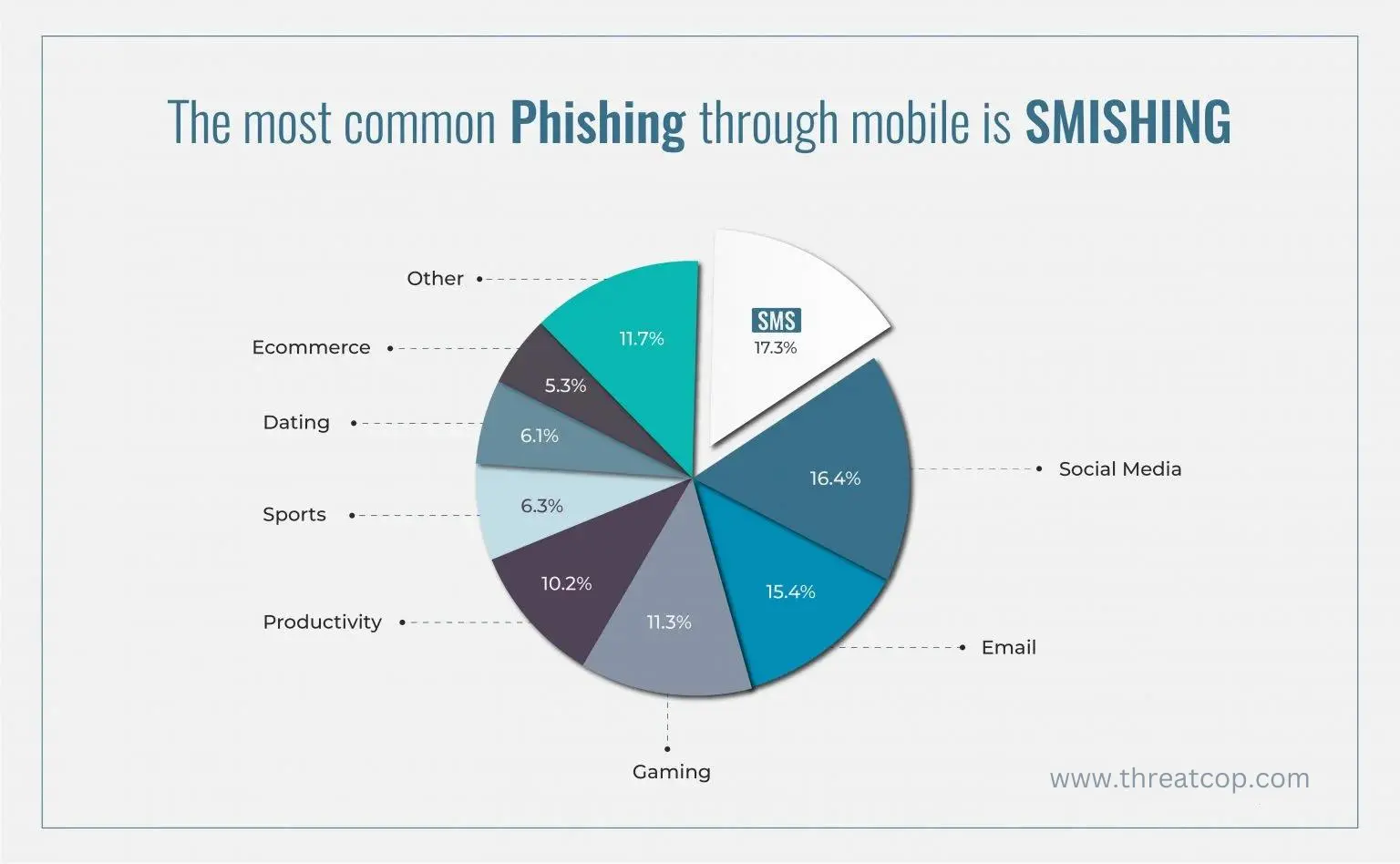
Smishing Awareness Training
Another prevalent technique is smishing, which involves sending deceptive text messages containing malicious links or enticing offers. Safety Detectives reported that 35% of the populace is unaware of SMS phishing schemes. Smishing awareness training familiarizes employees with common types of malicious text messages and teaches them how to report suspicious contact numbers and text messages.
Ransomware Awareness Training
In the first half of 2021, around 1097 organizations were hit by ransomware attacks. These attacks involve encrypting valuable data and demanding a ransom for its release. Ransomware awareness training aims to educate employees about malware delivery methods and how to prevent falling victim to such attacks.
Awareness is key to People Security Management
It’s crucial to raise awareness among employees about these various types of cyber threats and train them on how to identify and respond effectively. People security management is all about equipping employees with the knowledge and skills to recognize and report suspicious activities, organizations can significantly enhance their overall cybersecurity posture.
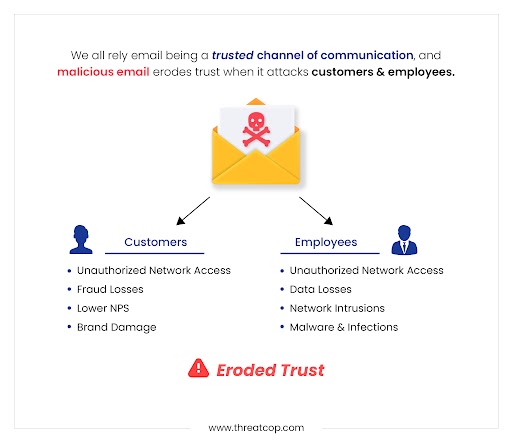
2. Threatcop DMARC
Recent data shows that today, almost 90% of all cyber-attacks are launched through emails. Another mentioned that 1.4 million threat emails were sent to employees. This means almost half of the total emails sent are spoofed emails. This signifies that Domain-based Message Authentication, Reporting, and Conformance (TDMARC) should be implemented without any second thought.
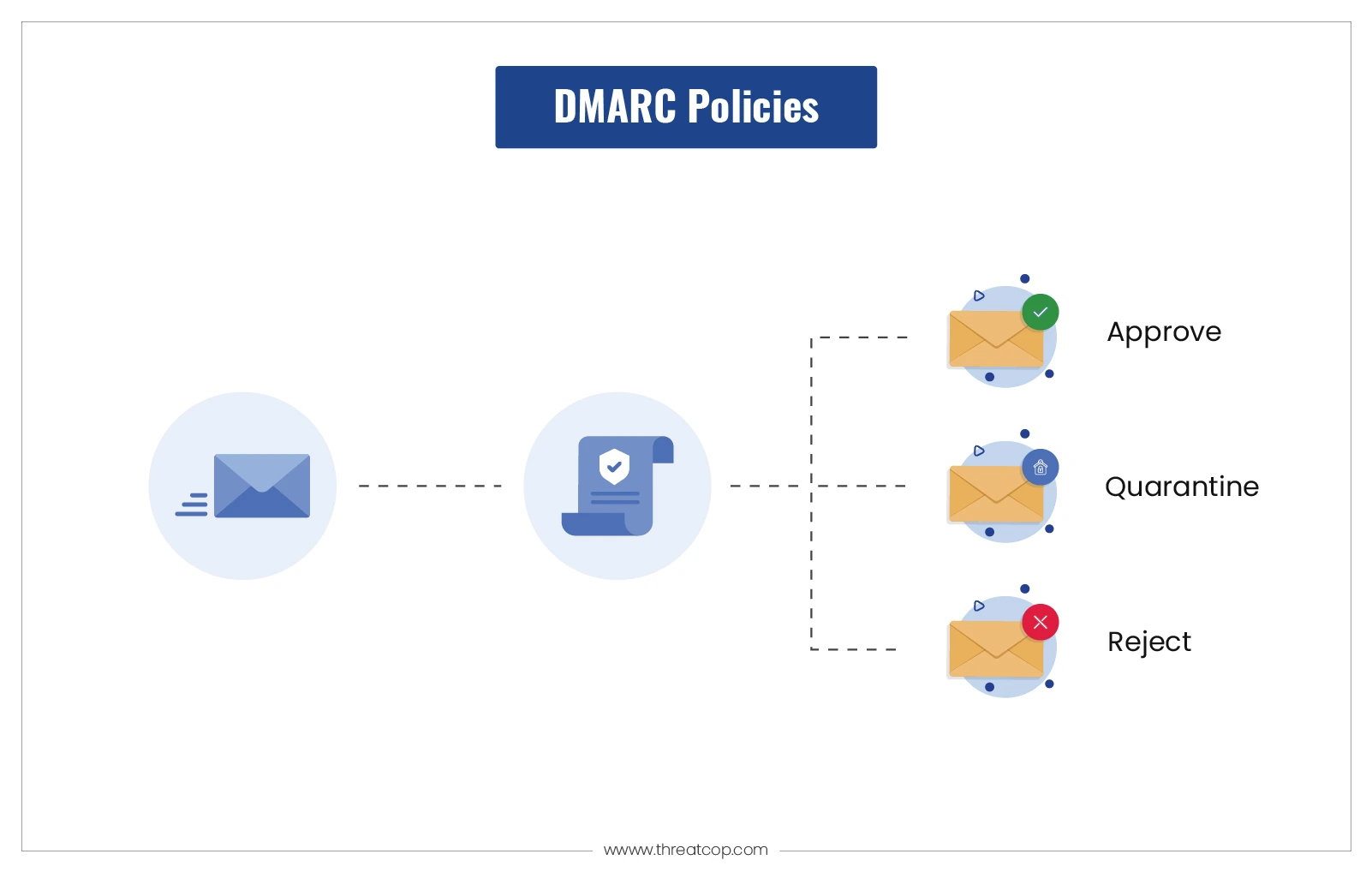
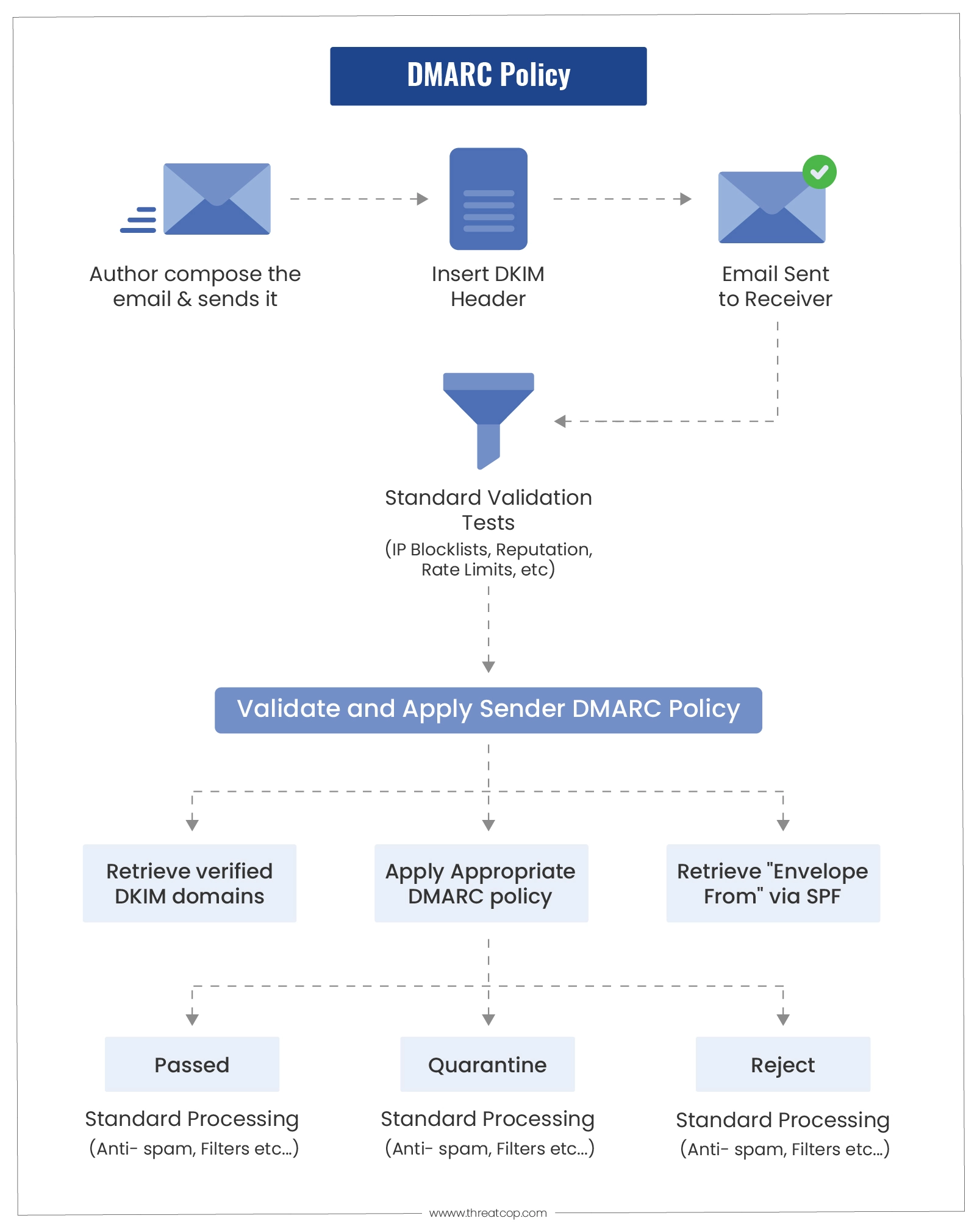
DMARC is a framework that helps protect senders from email spoofing and allows receivers to identify spoofed domain emails. It authorizes receivers to take action on emails that fail to verify and provides visibility into email flows.
Threatcop has secured more than 28000+ domains by implementing the Smart Sender Policy Framework (SPF) and Smart DMARC.
BIMI stands for Brand Indicators for Message Identification. It is an email authentication standard that allows businesses to display their verified logos in email inboxes. Google Workspace + TDMARC supports BIMI, and when used together, they can help businesses improve their brand reputation and protect their customers from phishing attacks.
This blue tick verification next to your brand logo provides an additional layer of assurance to customers that they are indeed interacting with a legitimate business. It helps establish brand authenticity and increases trust.
Types of Email Attacks
Spoofed Domain Attacks
These attacks mimic legitimate senders by creating emails that closely resemble messages from our domains. They are designed to deceive recipients with almost identical content, except for differences in the sending server’s IP address and the presence of malicious links, attachments, or illegitimate content.
Cousin Domain Attacks
Similar to spoofed domain attacks, these attacks mimic legitimate messages but use domains that closely resemble legitimate ones or obfuscate the domain with confusing subdomains. For example, they may use a domain like “pavpal.com” or create subdomains like “paypal.customer.service.com.”
Display Name Abuse
In these attacks, the attacker may use any domain but modify the “display name” portion of the “From” field to make it appear as if the email came from one of our brands or products. This can involve using a legitimate email address (e.g.,”support@threatcop.com”) or a functional role (e.g., “Threatcop Customer Service”).
3. TPIR
According to Deloitte, 91% of all cyber-attacks are launched through a phishing email. Forbes reported that on average, a single employee receives 14 malicious emails per year.
Thousands of businesses around the globe have lost money and data to successful phishing attacks. TPIR is an expertly designed solution that empowers your employees to identify and report suspicious emails with a click. Through Threatcop Phishing Incident Response (TPIR) Threatcop has successfully deployed 1100+ add-ons on users’ email platforms.
4. TLSM
Did you know? According to Infosec Institute, 69% of employees feel a lack of required cybersecurity training.
Threatcop Learning Management System (TLMS) is essential to build a security culture in an organization. According to a report by Ponemon, 13% of employees receive cybersecurity training quarterly. TLSM gives highly interactive security awareness content to enhance your employee’s training completion rate, situation-based assessments, and comprehensive user analytics. Threatcop has trained over 471,000 employees by using 600+ awareness content.
How does TLSM work?
Running Awareness Campaign
TLSM starts by running engaging and informative awareness campaigns within your organization. These campaigns aim to educate employees about various aspects of cybersecurity, including best practices, potential threats, and the importance of maintaining a secure work environment. This is not a boring practice at all as we have something for everyone through our different awareness content like cyber comics, Bollywood posters, and comic infographics.
Analyzing Employees Through Simulation
TLSM employs simulation exercises to analyze employees’ understanding and response to cybersecurity scenarios. Through simulating real-world cyber threats, such as phishing attacks or social engineering attempts, TLSM evaluates employees’ knowledge, skills, and decision-making abilities in a controlled environment. This analysis helps identify areas where employees may need further training or improvement.
Assessment and Reporting
TLSM conducts regular assessments to evaluate employees’ comprehension of security management concepts and their ability to apply them effectively. These assessments may include quizzes, interactive exercises, or practical simulations. The results of these assessments are then compiled into detailed reports, providing valuable insights into individual and overall organizational cybersecurity awareness and readiness.
ROI from Threatcop’s People Security Management
Unlock Unbeatable ROI with Threatcop: Your Smart Investment in People Security Management!
When it comes to investing in cybersecurity awareness solutions, calculating the return on investment (ROI) is essential to justify the expenditure. With Threatcop, you can expect a significant ROI that encompasses both financial and risk reduction aspects.
Threatcop provides an unmatched return on investment (ROI) by delivering value in both financial and risk reduction aspects.
Employee Empowerment
Threatcop empowers employees by reducing the time spent on managing security events and recovering from cyberattacks. This, in turn, increases staff productivity and allows them to focus on their core responsibilities, leading to improved operational efficiency.
Customer Loyalty and Credibility
With Threatcop’s robust cybersecurity measures, organizations can enhance customer trust and foster enduring client loyalty. By prioritizing data protection and preventing breaches, organizations can establish a reputation for safeguarding sensitive information, which in turn strengthens their credibility in the market.
Enhanced Risk Management
Threatcop’s advanced security solutions enable organizations to proactively manage risks associated with cyber threats. Our tools help in identifying vulnerabilities, implementing preventive measures, and responding swiftly to potential incidents, organizations can minimize the impact of security breaches and mitigate potential financial losses.
Regulatory Compliance
Threatcop ensures organizations remain compliant with relevant regulations and industry standards. By implementing comprehensive security measures and staying updated with evolving compliance requirements, organizations can avoid costly penalties and maintain a strong reputation for adhering to legal and ethical guidelines.
Improved Incident Response
Threatcop enables organizations to enhance their incident response capabilities. With real-time threat monitoring, prompt detection, and efficient incident management, organizations can minimize the time to resolve security incidents, reducing downtime and mitigating potential financial and reputational damages.
Build and improve Employee Cybersecurity culture
Threatcop’s training modules promote a culture of cybersecurity awareness among employees, leading to reduced human errors and security incidents. This saves costs related to incident response, recovery, and reputational damage.
Enhanced Brand Reputation Protection
By leveraging Threatcop’s DMARC solution, organizations safeguard their brand reputation by preventing email spoofing and domain abuse. This protects customer trust and reduces potential financial losses resulting from email-based fraud attempts.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
Threatcop’s People Security Management delivers tangible value by empowering employees, fostering customer loyalty, enhancing risk management, ensuring regulatory compliance, and improving incident response capabilities. This comprehensive value proposition translates into a strong ROI for organizations investing in Threatcop’s advanced ‘People Security Management’ cybersecurity solutions. To mark Cybersecurity Awareness Month, Threatcop collaborated with 31 respected CISOs and CTOs from prominent organizations. Together, we’re working towards a safer digital future.
Explore Here: 31 Cybersecurity Awareness Ideas from Security Leaders
Co-Founder & COO at Threatcop
Department: Operations and Marketing
Dip Jung Thapa, Chief Operating Officer (COO) of Threatcop, a leading cybersecurity company dedicated to enhancing people security management for businesses. With a profound understanding of cybersecurity issues, Dip plays a pivotal role in driving Threatcop’s mission to safeguard people’s digital lives.
Co-Founder & COO at Threatcop Department: Operations and Marketing Dip Jung Thapa, Chief Operating Officer (COO) of Threatcop, a leading cybersecurity company dedicated to enhancing people security management for businesses. With a profound understanding of cybersecurity issues, Dip plays a pivotal role in driving Threatcop's mission to safeguard people's digital lives.
