The frequency has also grown; according to Cybersecurity Venture, a ransomware assault occurs every 11 seconds. Certainly not the wow factor we desired, but remember that the standard for 2019 was 14 to 1. (i.e., every 14 seconds, an organization gets hit by a ransomware attack.) This post is about the most crucial ransomware statistics for 2022 and further relevant information.
Table of Contents
ToggleRansomware brings out the dark side of the Internet, and unfortunately, it is not limited to the Dark Web. It makes its way to innocent and inconspicuous people. As the name suggests, it aims to demand ransom from its victims. However, since the term also includes “goods,” it suggests that its roots are in the online world. The main tactics are phishing, extortion, and assuming false identities to obtain ransom. These loosely organized ransomware groups or individuals have used an infinite number of things to extort money.
Here are all the ransomware facts and statistics mentioned for the years 2021 and 2022. This blog is for a better understanding of ransomware attacks.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
Facts – 2021 and 2022 Ransomware Statistics
The following figures shed light on the range and escalating size of ransomware threats:
- Ransomware accounts for 10% of all breaches. According to the 2021 “Verizon Data Breach Investigations Report,” the frequency doubled in 2021.
- From January through July 31, 2021, the FBI’s Internet Crime Complaint Center received 2,084 ransomware reports. This marks a 62% increase year over year.
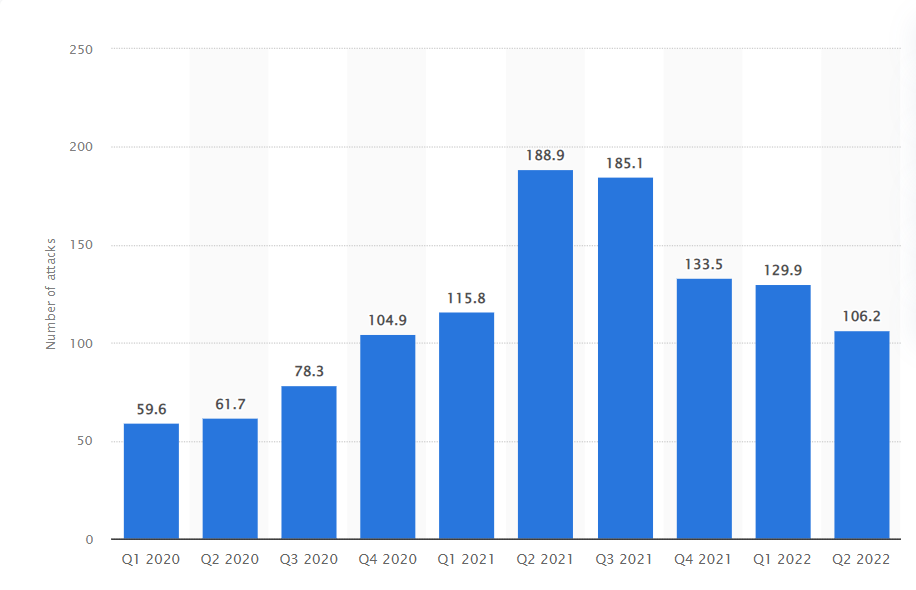
- A comparison of ransomware statistics from Statista says, over 80% of ransomware threats occurred globally in 2021 compared to the previous year. Around 1,500 breaches resulting in data exposure were reported in 2020, but by 2021 there were about 2,700 cases reported globally.
- In February 2022, the Cybersecurity and Infrastructure Security Agency said that it was aware of ransomware occurrences affecting 14 of the 16 critical infrastructure sectors in the United States.
- According to VirusTotal, the GandCrab ransomware family has been the most widespread, accounting for 78.5% of all samples and in general, 95% of ransomware samples are basically in Windows-based executable files data modules.
- 46% of ransomware creators pose as law enforcement agencies like the FBI. According to ransomware statistics from Stanford University, in 82% of these attacks, the victim’s system is locked without any file encryption.
Book a Free Demo Call with Our People Security Expert
Enter your details
A look at Ransomware trends for 2021 and 2022
There is a spike in the trend of ransomware statistics in 2021 and 2022. Among them are the following:
- Extortion: Previously, ransomware was defined as attackers encrypting data found on a system and then demanding a ransom in exchange for a decryption key. Data is exfiltrated by attackers through double blackmail. Without payment, the information can then be made available to the public on a website.
- RaaS: The days of each attacker having to build their own ransomware code and carry out a distinct set of operations are long gone. RaaS malware is a pay-to-use virus. It enables attackers to initiate and manage a ransomware campaign by providing the essential ransomware code and operational infrastructure.
- Unpatched systems are being attacked: This was not a new trend for 2021, but it is one that persists year after year. While some ransomware attacks leverage innovative zero-day vulnerabilities, the vast majority continue to exploit existing vulnerabilities on unpatched computers.
- Phishing: While ransomware attacks may infiltrate companies in a variety of ways, phishing emails were the most common root cause in 2021.
Recent Ransomware Statistics
As the entire world has shifted to the Internet due to the pandemic, the opportunities for ransomware attacks have tripled during this period. As a result, ransomware techniques and procedures have also changed. Ransomware used to be a singular activity in which attackers hacked into a single server and demanded a ransom for the encrypted files. However, because individuals and businesses had data backups and other extensive protections in place, it was easy to ignore these hacking and phishing techniques.
However, ransomware demands come in once the files have been moved to a separate location and the originals have been deleted. The data can be released as a result of this if the ransom has not been paid. This, in a way, is double extortion because businesses not only have to incur the risk of losing all the data but there may be no way for it to recover the data if the owner finds the device as well. The advent of cryptocurrency has also aided in further changing how ransomware operates. There are not many ways of identifying the source or ultimate destination of cryptocurrency anymore. This is why most of these ransom demands are made in cryptocurrency now.
The amount of this ransom has increased by 500 million dollars since 2020. This is a whopping 500% increase in ransomware demands and attacks since the last decade. This are the reasons why ransomware has been included in so many debates about cyber security these days.
Following are the most recent ransomware attacks that happened in the past and current year:
- The notorious REvil ransomware has attacked computer giant Acer, and hackers requested a $50 million ransom, which is said to be one of the highest ransoms.
- One of the biggest insurance companies, CNA Financial, announced that it had been the target of a cyber assault in March 2021. The attack was purportedly carried out by a gang called Phoenix.
- According to JBS USA, Colonial Pipeline was disrupted by a ransomware attack in May 2021, disrupting oil flow across the east coast. An attack on JBS USA, a meat processing company, in June 2021 limited the company’s ability to package meat products as a result of ransomware. Criminals using the REvil ransomware demanded $11 million from the corporation in ransom.
- Kaseya, a remote management software firm, was the target of a supply chain ransomware assault in July 2021. The assault is said to have been carried out by hackers utilizing the REvil ransomware platform.
- The Sinclair Broadcast Group was the target of a ransomware assault in October 2021, which disabled the network’s broadcast operations.
As mentioned, ransomware attacks have risen exponentially over the last three years. With the world trying to leave its mark online and reach a global consumer market, it has also opened them up to many risks. One such risk is ransomware attacks—the statistics on ransomware point to this possibility alone. Every website or cloud coming up is not necessarily as safe as we think it is.
These gaps and loopholes have allowed us to be vulnerable to such attacks on a much larger scale. However, increased discussions and innovations.
Final Thoughts: Ransomware Statistics
The statistics for ransomware have shown us that ransomware attacks have increased over the last three years. Moreover, after reading the complete article – it is perfectly clear. However, knowing the exact information on these kinds of attacks will better prepare the organization. Having these details in mind is better if businesses run into such situations.
FAQs: Ransomware Statistics
Ransomware payments are likely to be regulated by nation-states, according to Gartner. Gartner forecasts that by 2025, 30% of global governments will have policies around ransomware, up from 1% in 2021.
Sophos, a security provider, was the first to discover intermittent encryption inside ransomware in August 2021. Intermittent encryption encrypts just sections of files, causing them to look damaged. The method can avoid various types of existing ransomware defenses and detections.
In total, 79,000 security incidents have been analyzed, and 5,258 data breaches have been confirmed.
With so much cloud space and servers being fought over, ransomware attacks take advantage of not-so-secure servers and clouds to either phish them or physically infiltrate the device with all data and other information.

Senior Writer
Shantanu is an accomplished content strategist and technology enthusiast at Threatcop Inc. With a knack for translating technical intricacies into reader-friendly narratives, Shantanu contributes to making cybersecurity insights both informative and enjoyable for tech enthusiasts and general audiences alike.
Senior Writer Shantanu is an accomplished content strategist and technology enthusiast at Threatcop Inc. With a knack for translating technical intricacies into reader-friendly narratives, Shantanu contributes to making cybersecurity insights both informative and enjoyable for tech enthusiasts and general audiences alike.

Hi – do you happen to have Q1 and Q2 numbers for 2020?
Hi Quan, I have emailed you some related information. Hope that helps.
Thank you.