Today there is no organization that can claim they are completely safe from cybercriminals, including government agencies worldwide. These cybercriminals can target a particular government agency solely or they can be sponsored by the state. In this blog, we are going to look at some infamous and disruptive cyber attacks on government agencies that have impacted the target nation on another level of cybersecurity.
Table of Contents
ToggleThe cyber attacks on government agencies are mostly politically or economically motivated. Cybercriminals try to breach the government cybersecurity system to get crucial information. The data acquired from governmental agencies give the hackers an upper hand in damaging the prosperity of a nation.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
Cyber Disruption in the Ministry of Transport and Urbanization
On July 9th, 2021, the websites of Iran’s Ministry of Transport and Urbanization went offline due to cyber disruption. The websites of the ministry were not functioning for several hours. On the previous day, the same thing happened with the railways which led to the presentation of wrong information on the display boards. The tracking of electronic trains failed throughout the country. The messages on the boards informed of the cancellation and delays of trains throughout Iran.
Read more about Cybercrime: Rising Concern to Cyber World
Malware Attack on the G20 Summit in Paris
In December 2010, threat actors sent an email with an attachment of PDF files to the French Ministry of Finance. The PDF contained embedded malware. Once the received document was viewed, the system got infected with a virus, which forwarded the mail to the senior officials. This further infected their system with malware.
Type of Attack: Trojan Horse
Book a Free Demo Call with Our People Security Expert
Enter your details
This attack infected 150 systems out of 170,000 computers in the French Ministry. The embedded malware compromised the G20 data. The attack was discovered when someone noticed a strange movement in the email system. The news of the attack came out in February 2011, one month after the attack was discovered.

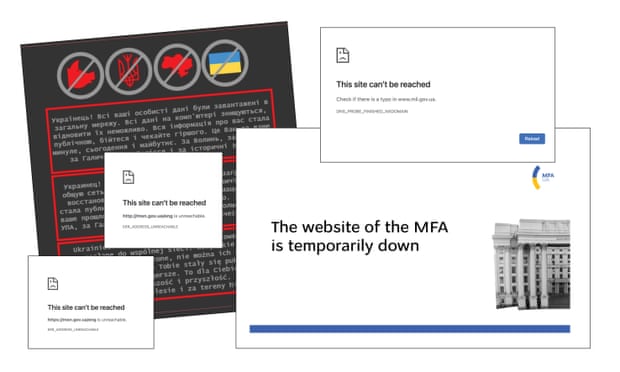
Ukrainian Government Targeted by Cyber Attackers
In February 2022, various government and banking sites came under a series of DDoS attacks. This attack occurred during a time when tension with Russia over territorial annexation escalated. Around 10 websites of the Ukrainian government, including the culture ministry, defense ministry, the foreign ministry, and two major state banks, were attacked.
Type of Attack: Distributed Denial of Service (DDoS)
The banks that got attacked were Privatbank and Sberbank, which led to the occurrence of problems in online payments and disrupted services in apps. Ukraine has blamed Russia for the stream of cyber attacks that disrupted the functioning of 70 Ukrainian government websites.
Earlier in 2017, Russia launched devastating cyber attacks on Ukraine using the NotPetya virus, which incurred damage of $10 billion. This virus was also known as the “wiper” that levied ransomware.
Read more about Powerful DDoS Attack Hits Hungarian Banks and Telecoms Service
Read more about Wiper Malware Threat Looms Over Tokyo Olympics

REvil Attacked Sol Oriens
Sol Oriens is a 50-person firm that was established for the purpose of consultancy to the U.S. Department of Energy’s National Nuclear Safety Administration. The cyber attack led to data theft of clients, but the company has denied any compromise of classified information or security-related data.
Type of Attack: Ransomware as a Service Attack
REvil, also known as the Sadinokibi Ransomware as a Service group, carried out a cyber attack on the veteran company. They distributed the company’s documents on the dark web that contained details of defense and energy development projects. This was found by a threat analyst of the company.
Read more about Ransomware as a Service: A Thriving Business for Hackers
Northern Ireland’s Parliament Buildings Under Cyber Attack
The IT department of the Northern Ireland parliament “Stormont” became a victim of a brute force attack. There were a series of attempts to log in to the email accounts of members of parliament. Many email accounts from the parliament were compromised. These accounts were later disabled by the IT department of Stormont.
Type of Attack: Brute Force Attack
The impact of this attack was that the threat actor got access to email accounts of people related to the parliament. The attackers are known as the ATP15 hacking group. This group was alleged to be an associate of Chinese intelligence that earlier hacked contractors of the UK government and stole military secrets.
Furthermore, the IT department instructed every individual to change their passwords and be vigilant for future cyber attacks. And they started working in collaboration with the National Cyber Security Center and Microsoft to monitor the situation and stop further leaks.

Attack on Russian Ministry of Defense
In July of 2021, the Russian Ministry of Defense suffered a “Denial of Service” attack. The attackers had exploited the system and disrupted the operations of the website. The websites were offline for about an hour before the attack was discovered.
Type of Attack: Distributed Denial of Service (DDoS)
This attack happened when US delegations were about to meet Russian delegates for a discussion on digital security. The attack was shocking because it breached the security of Russia’s Defense Ministry. This attack was believed to have been carried out from a foreign country.
Fujitsu Systems Breach Attacks the Japanese Government
The threat actors attacked the project management system of Fujitsu, which led to data leak from multiple government offices. The cybercriminal gained access to the “Project WEB” platform. It was found that the “Ministry of Land, Infrastructure, Transport, and Tourism” was impacted by the data breach.
Type of Attack: Data Breach
In this data breach, more than 76,000 emails were exposed that were registered on the domains of the ministry. The data that was stolen contained information about the equipment system, business relationships, etc. In the same stream of attacks, the National Cybersecurity Centre was impacted in which threat actors gained access to software and stole data from the air traffic control system.
Read more about Data Breach: Bye Domino’s, Hello There McDonald’s!
Read more about Third-party Data Breaches: A Rising Threat
Read more about 533 Million Facebook Users Affected in a Massive Data Breach
DarkSide Targeted Colonial Pipeline
The Colonial Pipeline is the largest operating oil pipeline in the United States and operates across 5,500 miles along the east coast. In May 2021, it went under a ransomware attack by the DarkSide hacker group.
Type of Attack: Ransomware Attack
In light of the discovery, the Colonial Pipeline company stopped all its operations to contain the attack. Under the supervision of the FBI, the company paid a ransom of $4.4 million in the form of 75 bitcoins. After the payment, the DarkSide hacker group provided the tool to the company so that they can restore its operations.
Read more about Ransomware Attack Hits a Major US Oil Pipeline
Wrapping UP
Cyber attacks on government organizations are highly destructive and damaging. Government agencies are supposed to secure their activities with the best IT tools and services. But, when any cybercriminal or hacker group attacks these governmental agencies, then it becomes disgraceful for the government agency. Thus, it is very important to incorporate extensive cybersecurity policies and practices within such agencies to prevent the exposure of national data.
